There has been a lot of conjecture in the past 40 years in patriot circles about the existence of government “round up lists”. Large-scale disaster and war planning exercises, like REX-84 (Readiness Exercise-1984) and Jade Helm 2015, have stimulated endless discourse about whether or not the government maintains a so-called “red list” and “blue list” of people that they deem to be dissidents who they might target for harassment, travel restrictions, or even detention without due process of law. Because any such lists would presumably be developed and updated under the wraps of a security classification and the Need To Know rule, this topic is understandably rife with conjecture, speculation, and even downright fabrication. So, in this essay, I will do my best to restrain my inner John Bircher and just stick to the facts. I’ll simply state the facts and add a bit of well-reasoned extrapolation, based on known technological trends.
The Real Face of FEMA
The centerpiece of all the speculation is the Federal Emergency Management Agency (FEMA). In my estimation, most of the chit chat on the Internet about “secret FEMA camps” is highly sensationalized. Civil internment is probably the lowest priority of any of FEMA’s contingency missions, and some would describe it as an almost hypotheticalcontingency.
Most Americans don’t realize it, but FEMA’s key mission is not disaster relief to the general public. Instead, their highest priority mission is assuring Continuity of Government (COG) following an external attack or following a widespread disaster that disrupts command, control, communications, and intelligence (C3I) assets and processes. If FEMA’s budget were ever drastically slashed, then the very last of their missions to be de-funded would be COG. In FEMA-speak, the COG part of their mission is listed under “National Continuity Programs”. They prefer to use the term Continuity of Operations (COOP), and that same term is used by the Department of Homeland Security (DHS). These taskings fall under the purview of FEMA’s National Continuity Programs Directorate and are organized per the National Continuity Policy Implementation Plan (NCPIP).
The COG/COOP mission was further clarified in 2007, under the National Security and Homeland Security Presidential Directive (National Security Presidential Directive NSPD 51/Homeland Security Presidential Directive HSPD-20. Therein, the term COG morphed into “Enduring Constitutional Government” (ECG).
A wiki article on NSPD 51 notes: “Conservative activist Jerome Corsi and Marjorie Cohn of the National Lawyers Guild have said that [NSPD 51] is a violation of the Constitution of the United States in that the three branches of government are separate and equal,with no single branch coordinating the others.”
A 2009 document prepared for the transition of the executive branch of government to the incoming Obama administration used the following euphemistic vanilla wording to describe FEMA’s COG/COOP mission:
“FEMA provides continuity services, not only for FEMA, but also for the entire Federal government, across the Nation, for common and asymmetric threats alike. It is essential for FEMA to maintain high-performance continuity services in the form of exercises, planning, standards, training, communications, and resiliency measures.”
In the same briefing binder there are also some more concrete but still slightly obtuse descriptions of FEMA’s COG/COOP responsibilities:
The criticality of continuity programs can be traced to three foundations. First, continuity programs, led by NCP, directly reflect the first of eight National Essential Functions (NEFs), “Ensuring the continued functioning of our form of government under the Constitution….” Second, continuity programs form the foundation of the seven remaining NEFs by ensuring that the government structures are in place to govern and support the economic, defensive, and social well being of the Nation. Third, continuity programs form the foundation of the National Response Framework (NRF), ensuring government structures at each tier (local, State, and Federal) are in place under all circumstances to sustain their essential functions, deliver essential services, and accept the assistance provided under the NRF. When government departments and agencies are inoperable and their continuity programs fail, the NRF will also fail.
NCP is responsible for ensuring Federal, State, local, Tribal, and territorial governments are capable of performing their essential functions during any situations that may disrupt normal operations.
Continuity Planning
NCP develops, publishes and trains continuity capability through Federal Continuity Directives and Non-Federal Continuity Guidance circulars, planning templates, and instruction for Federal, State, and local governments.
In a subsection, there is also this description:
Mount Weather Emergency Operation Center (MWEOC):
The MWEOC, located in Berryville, Virginia, is a continuity of operations (d) relocation site for several aspects of DHS and FEMA. The facility provides operational space for FEMA and DHS Emergency Relocation Group members to perform Departmental and Agency mission essential functions.
“A Billion Here, and Billion There…”
In recent Federal budgets FEMA’s Disaster Relief Fund has ballooned to around $7 billion per year, but that comes out of a more than $10 billion annual budget. So where is the other $3 billion spent? It’s spent on a whole lot of things, and many of them fall into categories like “administration, training, and interagency liaison”. Even though the big bunkers were built decades ago, still included in FEMA’s budget are many line items that relate to intelligence fusion, “national continuity”, and “continuity of operations”.
When FEMA Administrator Craig Fugate testified before the congressional Subcommittee on Disaster Preparedness about his agency’s 2015 $10.38 billion budget request, he pointed out that the FEMA is now working more closely with the DHS. Another key point that came up in the hearings was that 2015 was the first year that 25% of the agency’s budget was not formally set aside for law enforcement/terrorism prevention.
With its traditionally strong COG/COOP emphasis, FEMA long ago invested manybillions of dollars to ensure continuity of the executive branch of the Federal government. The Mount Weather complex is reportedly just one of several redundant deep underground bunkers. Some of these facilities were developed by other government organizations, partly for the sake of redundancy. Although they have established deep hardened bunker facilities with accommodations for Federal legislators and some Federal judges, their main focus is directed toward sheltering the White House staff and the directors and key staff of all of the Federal law enforcement agencies. Meanwhile, the U.S. military organizations each have their own infrastructures in place for protecting both their C3I networks and safely housing their general staff and related personnel.
Because of security classifications, it is difficult to know exactly how FEMA’s budget is being spent and how much of that might be directed toward contingency plans for housing of “displaced persons”. A lot could be hidden under that guise. Essentially the only difference between building a temporary city to house natural disaster refugees and one that is built to house detainees is the presence or absence of concertina wire perimeter fences. Parenthetically, I’d be curious to know if FEMA has ever put out Requests for Quotation (RFQs) for the manufacturers of concertina wire or razor wire, as measured in miles. However, here, I’m straying into speculation. So let’s get back to the facts at hand.
The J. Edgar Days
In the late 1930s, the FBI developed lists of individuals on cardstock index cards. One of these was the Custodial Detention Index (CDI), also known as the Custodial Detention List. This list was compiled between 1939 and 1941 under the “Alien Enemy Control” program. According to one published report:
“The Custodial Detention Index was a list of suspects and potential subversives, classified as ‘A’, ‘B’ and ‘C’; the ones classified as ‘A’ were destined to be immediately arrested and interned at the outbreak of war. Category A were leaders of Axis-related organizations, category B were members deemed ‘less dangerous’ and category C were ‘sympathizers’.”
After the United States entered World War 2 in 1941, these card file lists were put into operation. Large numbers of German, Italian, and Japanese nationals were rounded up and questioned. However, a disproportionately large number of Japanese were actually put in long-term detention—including thousands who were U.S. citizens living in coastal areas, ostensibly because the government “didn’t want to break up families.” This was a gross violation of civil rights, but given wartime exigencies it was hardly even questioned by most Americans until after the war was over.
According to research by the Federation of American Scientists (FAS), the FBI’s habit of building card catalogs of people did not end with World War 2. In the 1950s they moved on to building lists of Communist agents, subversives, and their fellow travelers. After the shocking revelations about Julius and Ethel Rosenberg, Claus Fuchs, and other nuclear weapons technology spies, this recordkeeping seemed well-justified.
By the late 1960s, when anti-draft protesters were a big concern for the executive branch, the FBI moved on to develop yet another list (actually a group of lists) called the Administrative Index (ADEX). This was before the FBI computerized their operations, so this was still a paper list on index cards. (It was perhaps later supplemented by Hollerith computer punched cards.) Additions to the ADEX were reportedly suspended in early 1978. But before it was discontinued and moved to their inactive files storage, the ADEX cards had merged several sublists, including the “Agitator Index” and the “Reserve Index”.
Automating The Lists
In the 1980s, following the lead of the early-adopting NSA and Atomic Energy Commission (AEC), the FBI moved into the computing age. Other than a few revelations about REX-84, very little has been revealed about any enemies lists that were developed in the 1980s and 1990s. Even REX-84 itself would have been nothing more than a obscure codename, if it were not for the much publicized Iran-Contra hearings that captivated the American public through what would have otherwise been a boring summer.
The following appears in Wikipedia’s entry on REX-84:
Transcripts from the Iran-Contra Hearings in 1987 record the following dialogue between Congressman Jack Brooks, Oliver North‘s attorney Brendan Sullivanand Senator Daniel Inouye, the Democratic Chair of the joint Senate-House Committee:
[Congressman Jack] Brooks: Colonel North, in your work at the N.S.C. were you not assigned, at one time, to work on plans for the continuity of government in the event of a major disaster?
Brendan Sullivan [North’s counsel, agitatedly]: Mr. Chairman?
[Senator Daniel] Inouye: I believe that question touches upon a highly sensitive and classified area so may I request that you not touch upon that?
Brooks: I was particularly concerned, Mr. Chairman, because I read in Miami papers, and several others, that there had been a plan developed, by that same agency, a contingency plan in the event of emergency, that would suspend the American Constitution. And I was deeply concerned about it and wondered if that was an area in which he had worked. I believe that it was and I wanted to get his confirmation.
Inouye: May I most respectfully request that that matter not be touched upon at this stage. If we wish to get into this, I’m certain arrangements can be made for an executive session.
Closely associated with REX-84 was Inslaw’s Prosecutor’s Management Information System (PROMIS) people-tracking software. For the sake of brevity, I won’t delve into that. But suffice it to say, PROMIS was fairly simplistic old technology that has been supplanted by much more sophisticated database search software.
Main Core
According to an article written for Salon magazine by Tim Shorrock in 2008, the NSA was the lead agency in developing a comprehensive personalities database called Main Core. This is the code name of a database containing personal and financial data of millions of U.S. citizens who are believed to be “threats to national security”. The Main Core data is compiled from the NSA, FBI, CIA, and other agencies. It is believed that this database (or we can safely assume its successor, under a different name) is still active and growing.
The latest conjecture is that in recent years the Main Core successor program has moved into social media sites, such as Facebook, using them as veritable vacuum cleaners that sweep up personal information. By applying some sophisticated algorithms, the Main Core apparatus determines threat levels and builds extensive “contacts webs” of familial ties and social relationships in an attempt to piece together organizational structures—both formal and informal.
Through a PRISM, Darkly
When taken in the light of the public revelations about the PRISM surveillance systemthat correlates private communications on the Internet, the implications of Main Core now go well beyond just “list keeping”. The presumed fusion of intelligence data that is going on has undoubtedly resulted in the creation of nested and prioritized lists of individuals to be tracked, travel-restricted, questioned, or detained, under a variety of crises.
Given the well-documented flaws in the FAA’s No Fly List, the errors that can be assumed to exist in Main Core’s successor databases could very well lead to the false arrest of hundreds or even thousands of people. Furthermore, if these databases were misused and applied to political reasons rather than legitimate counter-terrorism investigations, then it would open Pandora’s Box for tyrannical abuse.
Again, I discount the claims that there are “FEMA Camps” that have already been specially constructed to keep teeming masses behind razor wire. To the best of my knowledge, all that FEMA has done thusfar is to study and designate existing Federal military reservations as potential detention facilities. But there are almost certainly some very lengthy “round-up” lists of immigrants with ties to terrorist organizations. That in itself is perfectly justifiable, given the nature of 21st Century transnational terrorism. However, I fear that the names of tens of thousands of outspoken native born American citizens with high profiles have been listed in one or more databases as “persons of interest” by various agencies.
The fairly safe presumption of well-established Bad Boy lists that include native bornAmerican citizens troubles me, on several levels. Perhaps my biggest concern is that any such lists represent the intent of Federal officials to impose prior restraint, or worse yet their intent to flag “pre-crime” tendencies of law-abiding American citizens. This sort of segregation and prioritization forms the basis of a future “shopping list” for tyrannical bully boys, in the event of a national crisis. This crisis could be triggered by any number of events, including a natural disaster, a foreign terrorist attack, a domestic terrorist attack, an unattributable or misattributed cyber attack, a banking/equities market panic, a rigged/contested election (or a suspension of elections) leading to a constitutional crisis, et cetera.
Black List
If anyone reading this is politically active and is an outspoken champion of personal liberty, then it is probably safe to assume that you are already on some sort of list, at least a “watch list”. You might also be on a cyber black list, targeting you for disinformation/discrediting campaigns or perhaps for DDOS ping attack hacking. (It is no coincidence that DDOS ping floods are more frequently directed at politically outspoken blogs and web sites.) The key question is: what is your priority on those lists? If someone is a high priority for travel restrictions or detention, then their passport would be immediately flagged and they might not have the opportunity to leave the country via conventional means– through normal passport controls.
The recent events at the Malheur Wildlife Refuge in Harney County, Oregon illustrated that quickly removing the leadership of any political organization through targeted arrests can render it impotent or at least mute it in the court of public opinion. Think that through: Leaderless groups with redundant secure means of communication are the wave of the future. Activist groups like the Black Panthers were the 20th Century norm. Groups like Anonymous will be the 21st Century norm. But be aware that the use of social media and non-secure communications can be used by governments to build dossiers or even indictments against political organizers. (Facebook was specifically mentioned several times in the recent Malheur indictments.) It is best to avoid social media entirely, but if you must use it, then choose your words wisely!
You List
As I have written before, it is important that all prepared families keep their passports updated. You should also have a Plan B and a Plan C. If you suspect that you are high on a priority list, then you might need a Von Trapp family (The Sound of Music) walk-out escape plan. If you live near a coastline, then making the acquaintance of a deep sea trawler operator or a blue water yachtsman might be something to put near the top of your “to do” list.
Stay Vocal
I must urge my readers to not feel buffaloed into silence. If we allow ourselves to be frightened into political inactivity and Gray Man obscurity, then the tyrannical statist opponents of liberty will have won. Silence is tacit consent.
An acquaintance of mine who recently retired from blogging is fond of saying: “Never get on the bus.” I consider that sage advice. Just consider the fact that there are as many unregistered firearms in this country as there are adult citizens. We vastly outnumber those who might someday seek to enslave us. No attempt to round up a large segment of society will be successful if enough people refuse to register their guns, they keep their guns loaded, and they have the willingness to use them. We also have to well in advance commit ourselves to living through the angst of hiding any fellow citizens who come under persecution.
Lastly, we must never lose our vigilance about the encroachment of tyrannical new laws and policies. Take a few minutes to consider the Jews in the Attic Test.
This has been a heavy topic to consider, but I felt strongly convicted that it must be raised. Our liberty depends on it! – JWR(source)
This is a two part series which deals with critical issues associated with planned round-ups of potential resistance leaders and how to recognize when the extractions will happen. This is very valuable information as it will be important to not be where one is expected to be when the extractions commence.
The second part of this series will discuss the technology that will be employed to hunt down key resistance figures along with counter-intelligence techniques designed TO evade capture.
There are some universal principles that will be applied when key people are hunted down when the NSA/DHS decides that your Threat Matrix Score is too high and you must be extracted from society so that you cannot do any more damage to the emerging power structure that has hijacked our government.
The Historical Precedent of the Night of the Broken Glass

(It Happened In One Night)
In pre-holocaust Germany, Jewish businesses were singled out for physical destruction in an event called Kristallnacht (i.e. night of the broken glass). Hundreds of Jewish businesses were attacked on the same night.
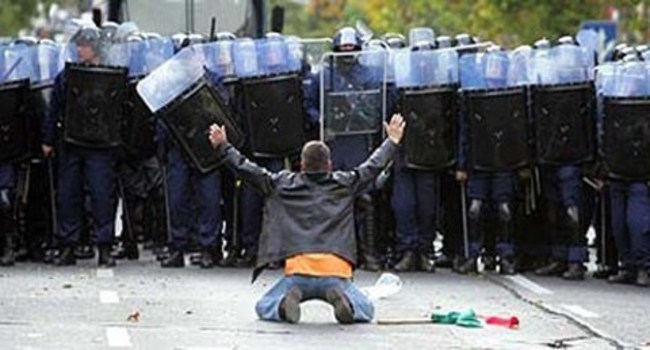
When the Holocaust began, in earnest, the Gestapo would target selected neighborhoods, for extraction, and then make their move, in the same general area, on the same night. If the area was large and exceeded the capacity to extract everyone in a given area, the neighborhoods would be sealed off, with nobody allowed in or out as systematic arrests were carried out. The times may change and the technology may be better, but the same Nazi blueprint would be applied.
Nazi Germany Revisited

Jade Helm appears to be following the same pattern as their Nazi predecessors. From the Liberty Brothers to my deep insider sources, the same message and the same Nazi scenario is emerging.
 When the extractions of political dissidents commences, the event will conform to the following pattern. Cell phone service will be blocked so the intended victims cannot warn each other when the event commences. In the ARSOF document, this is referred to as “surgical strikes”. The ARSOF dissident extractions will take place on the same night and with modern technology, it will be carried out with extreme efficiency.
When the extractions of political dissidents commences, the event will conform to the following pattern. Cell phone service will be blocked so the intended victims cannot warn each other when the event commences. In the ARSOF document, this is referred to as “surgical strikes”. The ARSOF dissident extractions will take place on the same night and with modern technology, it will be carried out with extreme efficiency.
There has been a lot written about the local police and participation in Jade Helm drills. However, it is not likely that the police will be going door to door beside ARSOF personnel, please consider the following.
____
Hi Dave,
I am a retired Deputy Sheriff but I still have regular contact with many from our department. They are not training with military forces as of yet, but they will soon be doing so. Some have been told that they will be assisting in the apprehension of key fugitives (aka terrorists). From memos and actual conversations, the job of the department will primarily be to provide a defensive perimeter that will prevent escape in a “nobody in and nobody out” approach. We know for a fact that other departments have been told similar things in briefings/memos held/conducted by the Department of Homeland Security.
I have been reading your articles for sometime now and I am convinced that LEO’s will be used as support personnel as “federal of military authorities arrest enemies of the state”. I do not remember seeing that you have written about local law enforcement and their role in what appears to be coming. Please take a look at this as there is an important story on this point. My family, some friends and I greatly appreciate your work.
____
This is what happened, for the most part, in South Carolina and this is precisely what the Gestapo did as they conducted mass arrests.
The Nazis almost always carried out their extractions at 3AM. Jade Helm announced that all of their drills would be carried out at from11pm to 4AM. Jade Helm leadership has also announced that they will be practicing “infiltration techniques”. And most know that the job of ARSOF is to extract or assassinate high value targets prior to invasion or occupation.
Precursor Events Prior to the Commencement of the Extractions
 The overwhelming belief among nearly all of is that an economic crash will be the precipitating event. When it is announced that the banks are “temporarily closed” and the bank bail-ins have commenced, many resistance leaders are living on borrowed time. From this point on, mass extractions, in this modern day version of the Night of the Broken Glass, could commence at any time. It is under this cloud of chaos that we will see this situation exacerbated by Fifth column attacks of shopping malls, schools and sporting events across all of the United States. The attacks will come from ISIS and MS-13 cells that have been embedded all over the United States. This will be the modern day version of shock and awe all designed to paralyze any potential response from the citizenry.
The overwhelming belief among nearly all of is that an economic crash will be the precipitating event. When it is announced that the banks are “temporarily closed” and the bank bail-ins have commenced, many resistance leaders are living on borrowed time. From this point on, mass extractions, in this modern day version of the Night of the Broken Glass, could commence at any time. It is under this cloud of chaos that we will see this situation exacerbated by Fifth column attacks of shopping malls, schools and sporting events across all of the United States. The attacks will come from ISIS and MS-13 cells that have been embedded all over the United States. This will be the modern day version of shock and awe all designed to paralyze any potential response from the citizenry.
Like Nazi Germany, the planned dissident extractions will take place on a single night in order to prevent foreknowledge and a potential push back.
Phase One Targeting: Who Are the High Valued Extraction Targets?
The number one targets will not be very many in the Independent Media as commonly believed. In order to neutralize this group, the administration would only have to pull the plug on the Internet. However, there are a few in the Independent Media who have contacts who are high priority targets and as such, these media figures would be sought after individuals as well.
I have had the “round-up” discussion several times over the past couple of years. The pattern is always the same and can be universally applied from country to country.
The number one group that will be targeted by the Special Forces intruders will be individuals with significant military experience who have the ability to turn a militia into a formidable fighting force.
Who would comprise such a group? Let’s start with the 260+ command officers fired by Obama. Some of these leaders are only pencil pushing administrators and would be of little use in an armed conflict. However, some of these men have significant combat experience and administrative organizational abilities which would make them high valued targets for all the obvious reasons.
The second most targeted group wouldbe veterans with counter insurgency combat experience from their Iraq and Afghanistan days. These individuals would be very well versed in the use of effective guerrilla warfare tactics and would have both the knowledge and needed experience to successfully employ asymmetrical warfare strategies against the encroaching UN forces, such as the 15,000 UN troops spotted in Texas yesterday. The occupation forces undoubtedly will be headed by the United Nations.
The third most targeted group would be individuals who have either military or agency (e.g. FEMA, Ft. Dietrich) experience with counter-insurgent use of biological and chemical weapons. This kind of experience would be worth its weight in gold because of the ability of certain individuals to inflict mass casualties on occupying UN forces. For those that know what they are doing, these weapons are not terribly difficult to manufacture and distribute. Counterinsurgency and counterintelligence officials from DHS and FEMA would have the knowledge to carry out such an asymmetrical attack. Long-time readers of The Common Sense Show may recall that I personally knew of a FEMA official who had experience in counterintelligence regarding biological and chemical weapons. Now, I understand why he and some of his former colleagues prepared a covert, isolated and well-prepared community to retreat to in December of 2012.
 I am told that the Ron Paul types will be taken into protective custody “for their own good”. These people are the not at the top of the list. However, the globalists do not want people roaming society who could be symbols of resistance. It is not likely that any harm will come to them because the powers that be do not want to create martyrs.
I am told that the Ron Paul types will be taken into protective custody “for their own good”. These people are the not at the top of the list. However, the globalists do not want people roaming society who could be symbols of resistance. It is not likely that any harm will come to them because the powers that be do not want to create martyrs.
I am told that interagency personnel will be targeted as well. What did Hitler do with the Brown Shirts? He killed them. The Bolsheviks did the same with retired military personnel in Moscow. Today’s interagency operational commanders will suffer the same fate because dead men tell no tales and there is plenty to tell if this intended coup against the United States is carried out. So, for some of you who swore an oath to the Constitution, you might consider looking at historical precedent.
With a few exceptions, the run of the mill political dissidents will factor into phase two which will involve relocation, incarceration and worse.
Conclusion
When the economy hits the skids, if you have reason to believe you are on the Red List, you best not be where the authorities can find you. Closing banks and economic chaos are signals that you should go into hiding immediately.
If one is targeted, can one avoid detection and evade arrest? The answer is a qualified yes. However, one has to possess detailed knowledge of the technology which could be used to locate you and what counter-surveillance strategies that you would have at your disposal. The good news is that one would not have to remain in hiding for a lengthy time. What we are speaking of here will result in civil war and Red List targets fade in importance with regard to this scenario when the shooting actually begins. Evading arrest will be the topic of Part Two of this series.
Finally, I have never seen a time when so many sources and so many people, in general, possess the same information about what is coming and when. In the Patriot community, by the end of the week, these facts will soon become common knowledge for those who possess the discernment to know when to listen. For most Americans, they will never know what hit them.
Fortunately, most massacres have warning signs for those who have the foresight to critically examine the times that we are living in. Albert Einstein was a man who understood history and he knew what was coming. Einstein possessed the ability to accurately assess the threat and he was able to move to safety. Will you?(source)